Most Popular Posts

Most Effective Tips for Your Mobile App Security
The number of smartphone users has been increasing every year across the globe. As a result, every business has to launch mobile applications to bring more convenience to their customers. Apart from delivering goods and services, companies also use mobile

How to crash iPhone & Mac OS with a Link: Safari Browser Exploit
iPhones and Macs are one of the most recommended devices for their security. macOS and iOS have always had a security advantage over android and windows. But is macOS and ios really that secure as Apple claims? Well funny enough

iCloudBrutter Tool: How to Hack to Recover Apple Accounts
Hacking Apple Accounts is like the holy grail for hackers. Apple is the biggest organization that has spent billions of dollars to enhance its securities and to secure the privacy of its clients. Back in Aug 2019, Google’s Project Zero

Gamers Should Prioritize Online Safety: 10 Tips to Stay Secure
Attention, fellow gamers! In the electrifying realm of online gaming, where every click is a step towards victory, and every second counts, you’re not just battling virtual foes; you’re fighting off real-world threats that could jeopardize your gaming paradise. From
Top 10 Android Cleaning Apps
Are you grappling with frequent storage issues, a slower device, or excessive heat? Maintaining your smartphone might be the key to resolving these problems. If you find yourself clueless about smartphone maintenance, worry not! Android cleaning apps are here to

Finding information about our target using Gmail – Gmail OSINT
In this blog, I’ll explain how to extract any user’s information simply by his or her Gmail address.Nowadays, Gmail is the only e-mail service that 99% of people rely on. The term “OSINT,” or “open source intelligence,” means extracting information
Top 10 Android Emulators
Emulators have become indispensable for those seeking a bridge between Android and their computers. Whether you’re a mobile gamer, an app developer, or just someone who prefers the versatility of their PC, Android emulators have you covered? In this list,

How to exploit routers with Routersploit
In this hacking tutorial, we will learn how to use the most popular hacking tool for hacking routers RouterSploit, a router hacking tool for automating the process of router exploitation. This tool is modeled upon Metasploit. You will find many
Top 7 Linux Ad Blocker Tools
In today’s digital era, the internet has evolved into our primary source of entertainment and information. Whether we’re enjoying our favorite shows, studying from popular sites, or searching for answers to our queries, the internet plays a pivotal role in

Top 5 Secure Email Services You Should Use
In the vast landscape of cyberspace, where information flows freely, your email account stands as a gateway to your digital world. Yet, with great convenience comes great vulnerability. The prevalence of cyber threats demands a reevaluation of our email practices,
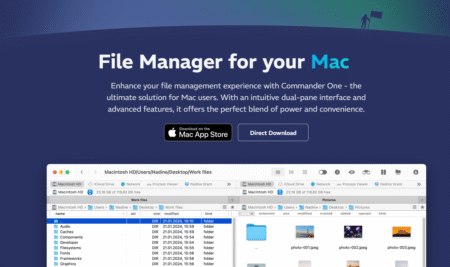
Commander One Review (2025): Dual-Pane File Manager for Mac
Commander One is a dual-pane file manager for macOS, developed by Electronic Team, Inc. It IS designed as an alternative to Finder, giving users more control, flexibility, and features for file management, remote connections, and workflow efficiency. Mac OS needs

How to detect bank phishing scams (12 Things banks will never do)
Recently the rise of bank phishing scams has grown to such a large extent that it is no longer possible to ignore the risks. Everyone is being targeted by spam and messages claiming to be from the bank. Hackers and