How to find anyone with Sherlock Tool
If you were looking for someone or if you want to find all the accounts associated with a particular username or password. The sherlock tool is for you. This is not the BBC sherlock homes coming and working for you, Unfortunately (I know I’m a big fan too). This is an automated tool that can find all the accounts associated with a particular username or email address automatically.
What is the Sherlock tool?
An automated Python script called Sherlock checks for all the accounts that have been made with the username and email ID you provide. This tool was upgraded by Yahya SayadArbabi, and the Original Creator of sherlock is Siddharth Dushantha.
Sherlock is quite efficient and versatile. You can give many usernames as well. Additionally, you can also try the custom options mentioned below. Do note this tool is for educational purposes only. Sherlock is excellent for information gathering. Do make sure you read the help section for all the possible parameters you can use with sherlock.
Installation Steps
NOTE: This tool requires the installation of Python 3.6 or higher to work. Make sure to install Python. The latest version of Kali Linux has Python installed by default.

To clone the github repo use the following command in kali linux terminal:
git clone https://github.com/sherlock-project/sherlock.gitNow change the working directory to sherlock folder:
cd sherlockYou need to have python installed on the system to use this tool install the other software requirements with the following commands:
python3 -m pip install -r requirements.txt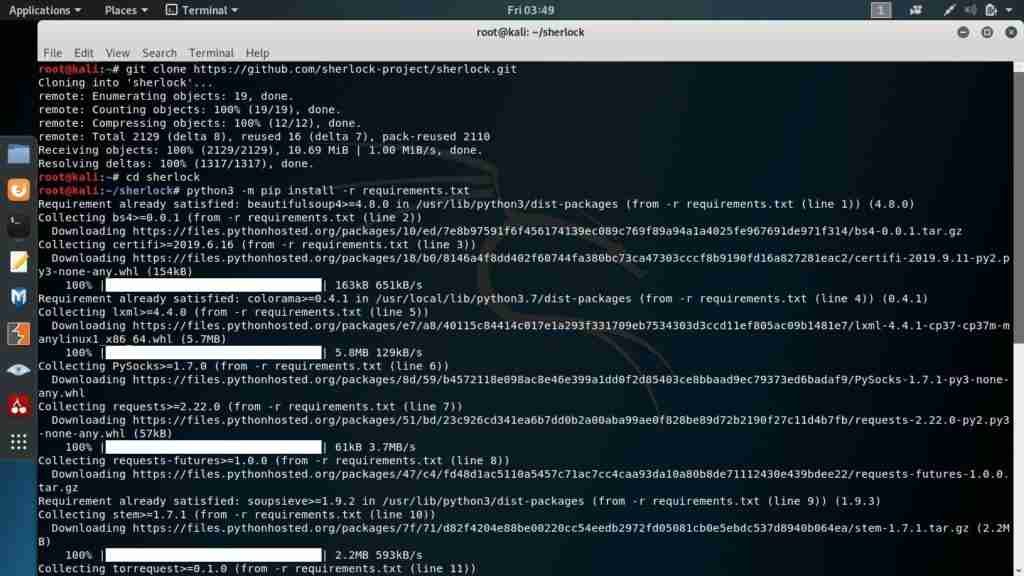
Now there are many options which are available with the tool:
In order to see all the options, just type the following:
python3 sherlock.py -hThe -h after sherlock.py shows all the help options:

The most used options will be the following:
Search for only one user:
python3 sherlock.py user123To search for many users:
python3 sherlock.py user1 user2 user3All of the accounts found will be stored in the respective text files with the corresponding username (e.g user123.txt).
The default output is too messy, so I prefer using the following parameter.
--print-found
This parameter displays only the websites where the account was found.
So let’s try a practical example.
Here I am using my username nightfury007 in sherlock
So in my case, the command becomes
python3 sherlock.py nightfury007 –print-found

And viola you can see all the sites having nightfury007 username. Do note that not all the accounts are mine. This tool only shows which sites have the following username.
In my case, it was nightfury007.
You can use this tool for social engineering and passive information gathering. You can also use advanced options in sherlock to becomes anonymous by using proxy and tor. This can help you with stealthy reconnaissance.
Commonly asked questions:
Q1. Can this tool give me passwords for the accounts?
No, it only checks if the username or email exists on the list of sites in sherlock.
Q2. Who made the sherlock tool?
Yahya SayadArbabi upgraded this tool, and Siddharth Dushantha is the original creator of Sherlock.
Q3. How many websites are present in this tool?
We update websites regularly. The number of websites is too many to count. You can simply check them.
Q4. How accurate is this tool?
Well, what this tool does is it finds all websites with the username you provided. However, that username might not necessarily be of the person you are looking for. Therefore, it all depends.
Do not use it for any illegal purposes. You are responsible for your own actions with this tool.
Hope you liked the article do share and donate if you loved the posts. You can get all the information in the custom requests section.