How to sniff passwords with net creds
If you have not heard of net creds, then do not worry. It is not a mysterious hacking tool. It is just a Python-based sniffing tool which is ideal for sniffing plaintext passwords and password hashes from a network. If you have read my previous tutorials on password sniffing, you can be sure that hacking passwords is very easy if you have the password hash.
In this Kali Linux Tutorial, we will teach you how to use Net Creds and launch a Man in the middle attack on your local network. As you can guess, this hack works locally and not over the internet. Both you and the target victim need to be on the same network for this hack to work.
What is sniffing?
Sniffing is the process of monitoring and capturing all the data packets passing through a given network. Sniffers were originally meant to be used by network administrators to monitor and troubleshoot suspicious network traffic. However, nowadays, hackers use sniffers to capture data packets containing sensitive information such as passwords, account information, etc.For the sake of convenience, I will be using a Kali Linux machine as my attacker and a windows machine as my targetYou can download the Net Creds Tool from the GitHub repository
Since Kali Linux, by default, has all the things you need for hacking, it makes it much easier to use kali for sniffing passwords.
Warning: This article is for educational purposes only. The Hacking world is not in any way responsible for any illegal activities you do. We will not be liable for any misuse of information done on your end. Please read the disclaimer properly.
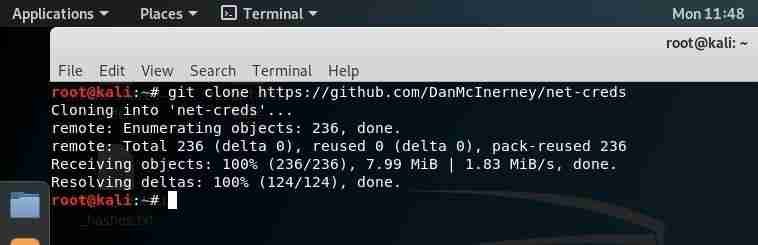
Step 1: Clone the password sniffing tool
On Kali, you can just use the following command to download net creds:
git clone https://github.com/DanMcInerney/net-creds
Step 2: Starting the Attacker machine(Kali Linux)
Change the directory with the following command:
cd net-creds
To start the sniffing attack
Execute the net creds script with the following command:
python net-creds.py -i eth0
You need to choose the correct interface, here in my case I have used -i eth0 as my interface.

Step 3: Wait for the victim to log in
When the victim logs in an unprotected website, which sends passwords in the form of plain text. The password will be captured, and the hacker will easily hack the account passwords.
- The below image shows the sniffed data in GET & POST request format of the HTTP protocol. From analyzing this traffic, we can easily see the plain text password you see below.
For this demo, I used a fake bank website. This attack only works with websites having HTTP traffic.

Commands you can use in net creds:
- Auto-detect the interface for sniffing
sudo python net-creds.py
- Choose eth0 as the interface for sniffing
sudo python net-creds.py -i eth0
- Ignore packets to and from 192.168.0.2
sudo python net-creds.py -f 192.168.0.2
- Read from pcap file which you have captured
python net-creds.py -p pcapfile
Features of net-creds for Sniffing Passwords
Net creds is a really powerful hacking tool because it can sniff the following formats and protocols directly from a network interface or from a PCAP file and expose all the sensitive information being transferred on the internet. These protocols are plain text-based and thus should not be used in the first place.
- URLs visited
- POST loads sent on the network
- HTTP form logins/passwords used
- HTTP basic auth logins/passwords setups
- General HTTP searches
- FTP logins/passwords in plain text
- IRC logins/passwords in plain text
- POP logins/passwords in plain text
- IMAP logins/passwords captured
- Telnet logins/passwords
- SMTP logins/passwords
- SNMP community string
- NTLMv1/v2 all supported protocols: HTTP, SMB, LDAP, etc.
- Kerberos
How to prevent a MITM attack
- The first defense against sniffers is strong security implementations on a website level. A website must have an https certificate. This way the traffic is always encrypted and even if the attacker gets the data. He will have a hard time decrypting it.
- Antisniffer and antivirus tools to detect the use of sniffers on your network.
- Regular updates to operating system and browsers
- Using only safe websites.
Commonly asked questions about sniffing with net creds
Q1. Is using this attack on public wifi legal?
No, it is not. It is only for testing purposes. This article is an educational article; please use it with the same intent.
Q2. Can I hack anyone over the internet?
No, this attack words when both the attacker and the victim are on the same network.
Q3. Can I hack android devices with this attack?
Yes, if the victim is using websites that do not have HTTPS protection then yes you can hack them with this method.
Q.4 Can I use this attack with an android device?
Of course. You can use kali nethunter or termux to install and run this attack. I will also make an article on how to do an SSL strip with zanti. So stay tuned.