
Facebook Account Hacking – Top 5 methods
Are you sure your Facebook account is safe from prying eyes? Think again! Today, we’re diving deep into the world of Facebook security to uncover the surprising vulnerabilities that could compromise your privacy in ways you never imagined.
Now, hold on! This isn’t your typical hacking guide. We’re not here to divulge dangerous techniques or shady shortcuts. Instead, we’re shedding light on the lesser-known aspects of Facebook’s security loopholes that might just leave your jaw on the floor.
We know what you’re thinking: “I’ve set a strong password, enabled two-factor authentication, I’m good to go!” Well, buckle up because the truth might astonish you.
But wait, there’s more! We’re not just stopping there. Have you heard about the alarming rise of social engineering scams targeting even the most vigilant users? Learn how hackers use psychological manipulation to gain access to your account, and most importantly, discover the foolproof ways to protect yourself against these cunning tactics.
This isn’t a scare tactic; it’s a wake-up call! Your Facebook account is more than just a profile; it’s your digital identity. And safeguarding it starts with knowledge.
Let’s start by setting the record straight: hacking into Facebook or Instagram accounts isn’t as simple as a few clicks on random tools or websites. It’s time to debunk the myth that typing an email address into a tool will magically reveal someone’s password. Trust me, if it were that effortless, Facebook would have closed shop ages ago.
Scouring Google might tempt you with promises of free tools that claim to unlock any Facebook account, but let’s be real — falling for these traps takes us to a whole new level of gullibility. Congratulations, but not the good kind! These tools lead to dead ends and empty promises, offering a false sense of control over something as intricate as hacking.
Identifying these fake Facebook hacking sites is crucial. They often share common traits:
- Slick, User-Friendly Interface: A deceptive simplicity where you input a user ID and hit ‘hack.’
- Phony Success Claims: They boast about cracking the password but conveniently fail to reveal it.
- Misleading Links: They redirect to surveys, pesky ads, or worse, prompt downloads of malicious software.
All these sites share one undeniable trait: they don’t work. NOTHING!
But why does this matter beyond the obvious?
Well, it’s more than steering clear of these faux promises. Understanding their deceptive tactics is the first step in safeguarding yourself against digital threats lurking in the shadows of the internet.
This is just the tip of the iceberg! Unraveling the complexities and unveiling the true steps to fortify your Facebook security is a journey that’s worth taking. Buckle up because in this blog, we’re delving deep into the intricacies of Facebook security. Let’s unravel the truth and equip ourselves with knowledge that truly protects.
Understanding the intricate workings of Facebook isn’t merely about trying to hack it. It involves comprehending the website’s functionalities, diving into the database management systems, dissecting the scripts, deciphering the use of cookies, and understanding the coding languages that build the platform’s foundation.
Yet, hacking into Facebook or Instagram isn’t a walk in the park.
It entails locating vulnerabilities within the system, coding exploits to navigate obstacles, and attempting to breach Facebook’s defenses to gain system privileges. Even decrypting their encrypted passwords poses a monumental challenge. Setting a backdoor for future access while covering tracks to evade detection? It’s a daunting task bordering on the brink of impossibility.
But hold on a second. Despite the technical complexities involved, there’s a narrative among us. You might have encountered someone, maybe that kid next door, who boasts about effortlessly accessing anyone’s Facebook password. However, their prowess doesn’t lie in coding exploits but rather in the realm of social engineering.
Let’s face it; while technology fortifies itself with robust security measures like the seemingly impenetrable 256-bit encryption, it’s the human factor that remains the Achilles’ heel. Users, often oblivious to the inner workings of Facebook or Instagram’s security measures, unknowingly nullify the platforms’ efforts through their inadvertent actions.
“People often represent the weakest link in the security chain and are chronically responsible for the failure of security systems.”
This quote is from the book Secrets and Lies: Digital Security in a Networked World, written by well-known cybersecurity expert Bruce Schneier
So, how can one’s Facebook or Instagram account be hacked, and more importantly, what measures can be taken to safeguard against such intrusions?
Here are the Top 5 methods used to hack facebook or any other social media accounts.
1. Phishing
Phishing involves luring users into providing their login details through deceptive means. Attackers create fake login pages resembling Facebook’s site, enticing users to enter their credentials. These fraudulent pages capture the entered information, granting hackers unauthorized access to users’ accounts. By presenting urgent or enticing messages, phishers manipulate users into divulging their login credentials unwittingly. Essentially, phishing within Facebook hacking tricks users into sharing their login information, enabling hackers to compromise their accounts for malicious purposes.
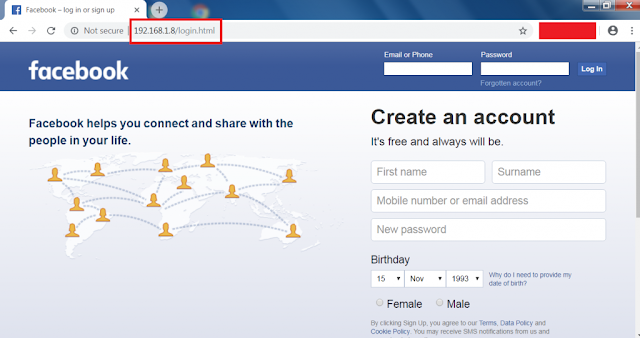
Below is a picture of Facebook login page, but just take a look at the url. Did you notice something? The URL in here is not “https://facebook.com/login”, its “192.168.1.8/login.html“. This is the most common way you can find if a website is legit or fake.
2. Reset The Password/Recover Account
Resetting passwords can be an avenue for unauthorized access to Facebook accounts, especially when the attacker has familiarity with the victim. If the attacker knows the victim’s email, they often leverage the ‘Forgot Password‘ option. Upon entering the victim’s email and account identification, they choose ‘This is my account.‘
If prompted to reset via email, this tactic might not succeed for the attacker. They then select ‘No longer have access to these?‘ Based on Facebook’s current policies, the attacker might need to identify friends in pictures, respond to security questions, or input an unlinked email address.
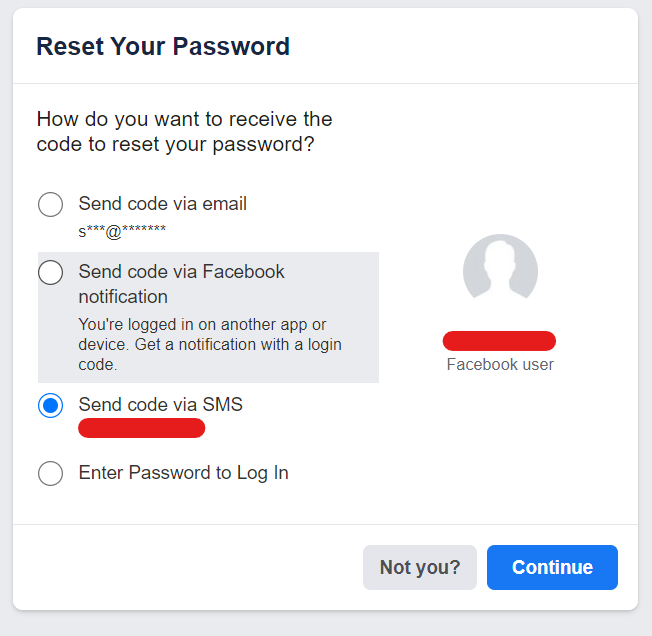
To safeguard against such attempts, using a dedicated email solely for Facebook and refraining from displaying it on the profile is crucial. Additionally, crafting intricate security questions—avoiding easily guessed information from personal interactions or public posts—is vital. Steer clear of pet names, anniversaries, or familiar figures, as these details are susceptible to guessing.
3. Easy Passwords
Currently, individuals are increasingly cognizant about their password choices; however, reliance on easily remembered yet predictable passwords, such as birthdays, mobile numbers, or nicknames, poses a substantial risk due to their vulnerability to hacking.
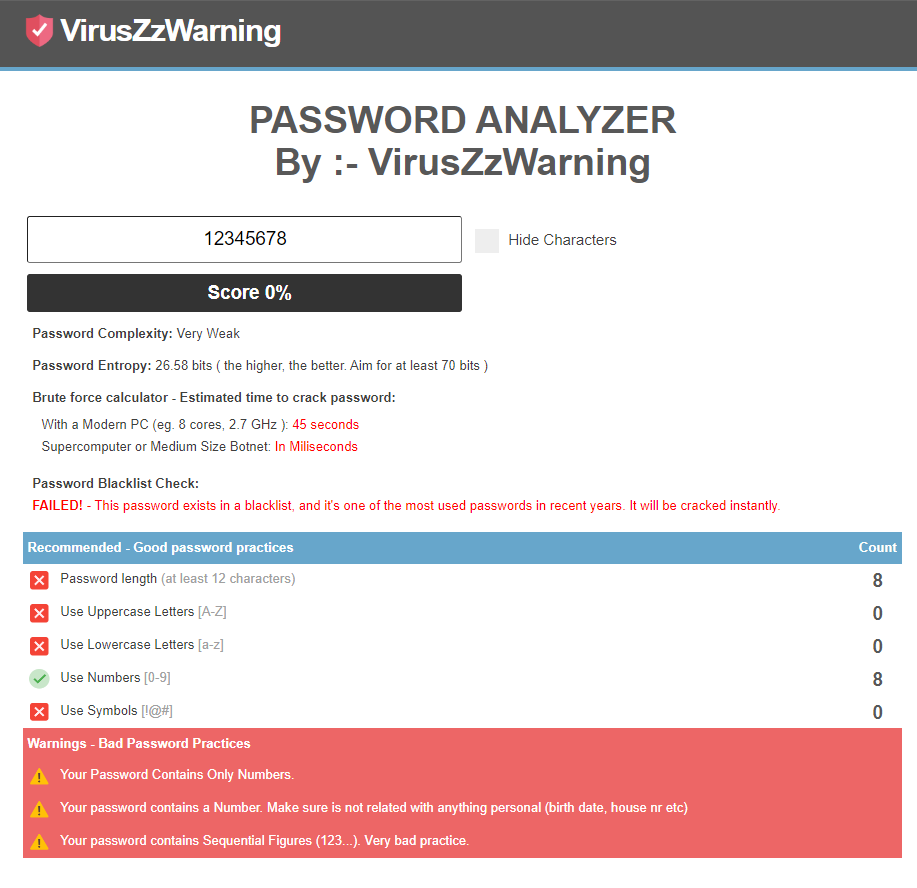
To ensure robust security, the initial step involves selecting an unconventional password. Optimal passwords are at least 13 characters in length, incorporating a mix of uppercase and lowercase letters, numbers, and special characters like @, *, #, or ?. Valuable guidance on crafting secure passwords can be found here.
Critical to note is the avoidance of writing down passwords or any personal information. Hackers often scour through discarded material, including bins, in search of personal data.
4. Man in the Middle
Imagine an attacker closing in on their target, employing a sneaky tactic called a man-in-the-middle attack (MITM). They create a deceptive, free Wi-Fi network, tricking unsuspecting users. Once a target connects, the attacker pounces, stealing valuable credentials. Tools like Wi-Fi Pumpkin make it shockingly simple to set up these rogue access points.
As soon as the victim links to this Wi-Fi, the attacker gains access to all the data packets traveling between the user and, say, Facebook. This occurs because everything flows through the attacker’s Wi-Fi hub. Tools such as Wireshark and Ettercap become potent aids in this intrusion.
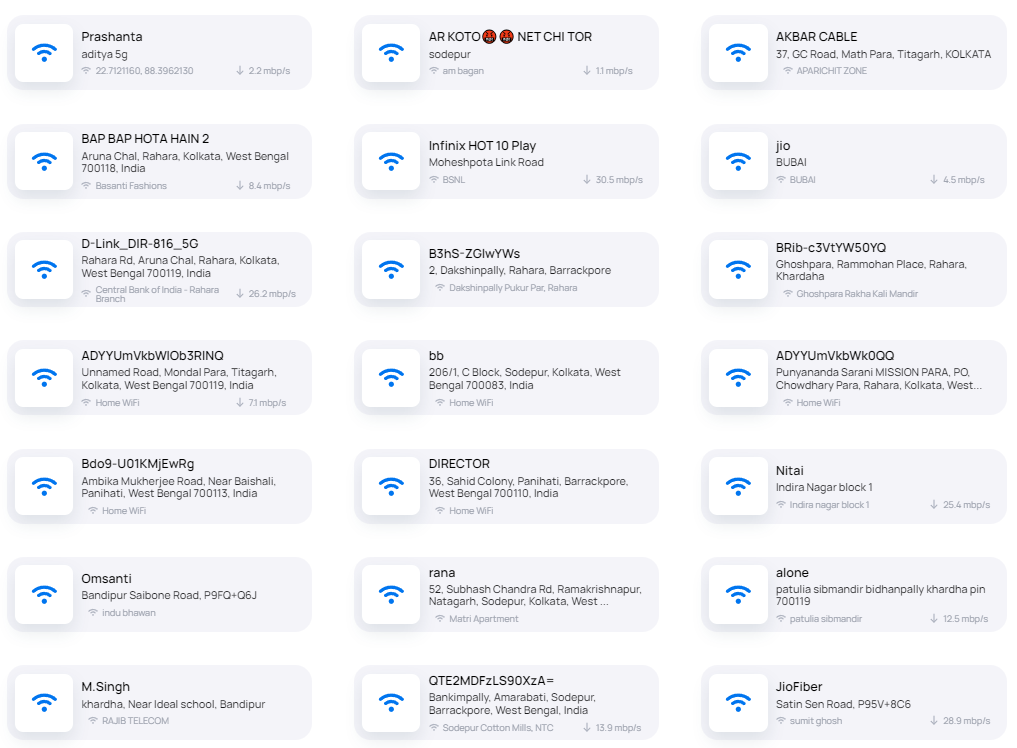
So, how does one safeguard themselves from such a malicious attack?
Firstly, steer clear of open and unsecured Wi-Fi networks. Avoid connecting to any networks that seem out of place—a “Google Starbucks” popping up where there isn’t a Starbucks nearby should raise suspicions. Attackers rely on our devices automatically connecting to familiar network names.
If you encounter issues connecting to your usual Wi-Fi, take a peek at the nearby networks. A duplicate of your Wi-Fi network might signal an attacker using tactics like an Evil-Twin setup or similar assaults.
Moreover, if your router prompts you to enter a password for firmware upgrades unexpectedly, beware. It could be a ploy to nab your credentials.
5. Looking for Passwords
Protecting our Facebook accounts involves staying vigilant against potential hacking attempts. One way attackers gain access is by observing as we type in our passwords, whether through someone peeking or even a hidden camera.
Another method involves physically accessing a person’s personal computer. Many individuals find it convenient to save their login details on browsers for quick access, yet this habit poses a risk. Attackers, if they get their hands on the victim’s computer, often navigate to the browser’s advanced settings or privacy sections to uncover these stored credentials easily.
To enhance our security, it’s crucial to be mindful while entering passwords, ensuring no one is observing us or using a camera to capture the input. Also, reconsider the habit of saving login details on browsers as they can be remotely stolen through malicious web applications. Moreover, it’s best to avoid typing passwords in public places or accessing social media accounts on shared or public devices, like cyber cafes, to minimize the risk of unauthorized access.
Conclusion
This guide is tailored for beginners entering this domain. It’s crucial for everyone to grasp how Facebook, Instagram, and other social media accounts might be compromised, along with essential safety measures. Our intention is purely educational. Unlawfully accessing Facebook, Instagram, or any other account constitutes a serious offense. We emphasize that we hold no responsibility for any illegal actions undertaken. To be clear Facebook hacking in current day is near to impossible, without someone falling for the above mentioned topics.
Internet is vast and it’s your responsibility to be secure ❤.
-VirusZzWarning



15 Comments
My friend Facebook account hacked recover please help me sir
Jaswant Singh mujhe account hacked kar na he
My facebook account hacked please recover the account
Dear sir My account fecebook account hacked please help me..
Ak id lena tha
I need help. a woman stalked me online for over a year then she got my husband in her game and they stole everything I own. I need access to their facebook accounts to prove they did this to me. Can you help?
I want to know how to hack another account Facebook
No.
My facebook account hasbend hacked please recover sir
Hey
He is a hacker he hacked id and post xxx cideos and negative comments to people
Hello,
Forgot my access:
I’ve forgotten my password for a while now and don’t know if my Facebook account is even blocked now.
Username: Benadin Delibasic
ID: 100075136093552
https://www.facebook.com/profile.php?id=100075136093552
https://www.facebook.com/groups/566377424701691/
created a page back then as GV.
PLEASE
can you help me?
How can I hack a Facebook
My friend scam in my Facebook account hack please recover my account
Mujhe bhi account hack karan hai