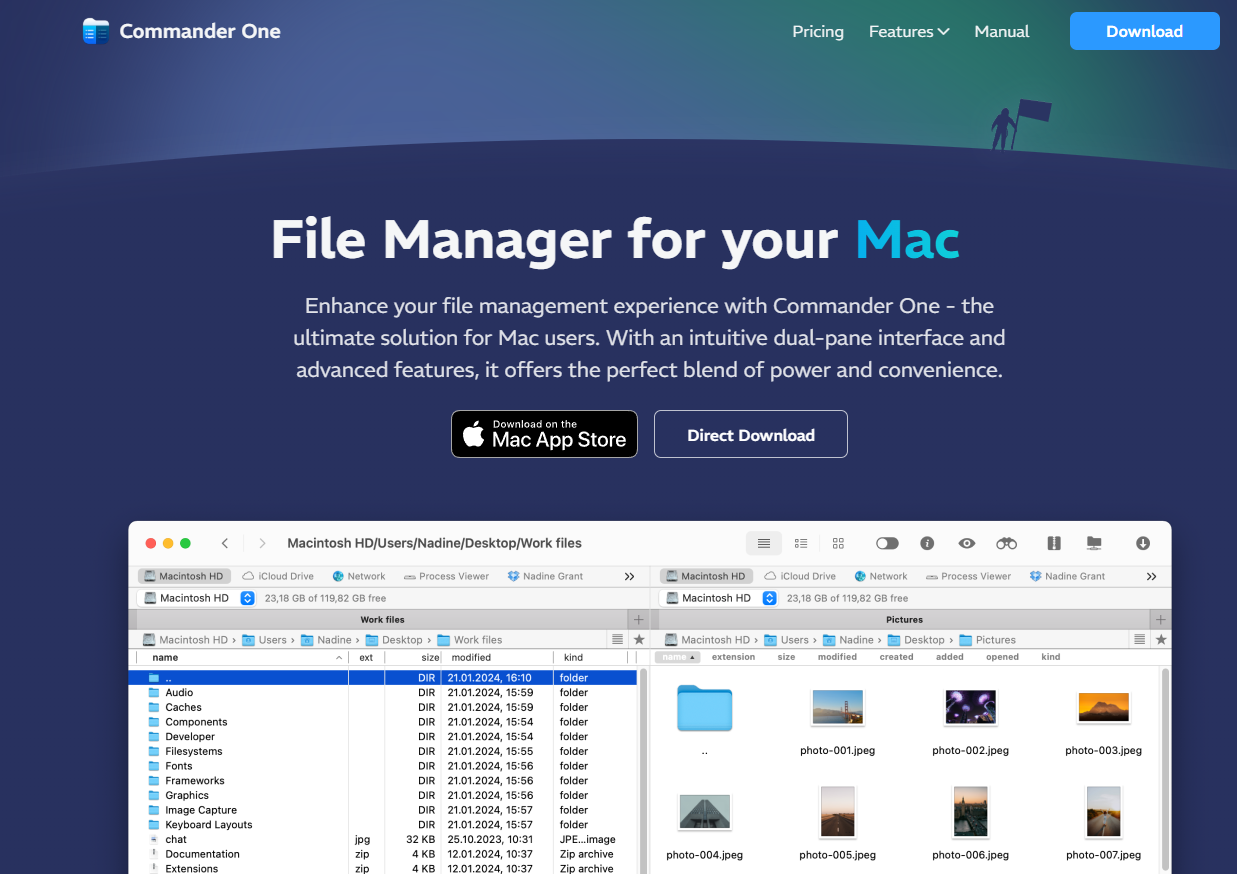
Commander One is a dual-pane file manager for macOS, developed by Electronic Team, Inc. It IS designed as an alternative to Finder, giving users more control, flexibility, and features for file management, remote connections, and workflow efficiency. Mac OS needs …
You tap your phone, grab your coffee, and go – a simple, convenient NFC payment. But lurking behind that seamless transaction lies a realm of security concerns and questions. Is your tap-and-pay method really safe? Let’s delve into the world …
Are you sure your Facebook account is safe from prying eyes? Think again! Today, we’re diving deep into the world of Facebook security to uncover the surprising vulnerabilities that could compromise your privacy in ways you never imagined. Now, hold …
Imagine this: with just one click, your entire system could be exposed to alarming cyber threats. Welcome to the realm of Local File Inclusion (LFI), a hidden peril that demands urgent attention in the digital landscape. In the realm of …
The internet is huge, and we spend a lot of time on it. But there’s a sneaky danger hiding there called XXS vulnerability. It’s a problem in cybersecurity, but it affects a lot of websites we use every day. From …
Empowering analysts and security researchers, IDA Free stands as a potent tool for analyzing and reverse-engineering binary code. Esteemed among professionals, it garners popularity within the realms of security research and malware analysis. This blog post aims to illustrate the …
Cybersecurity research is a constantly evolving field, demanding innovation and creativity in systematically probing system vulnerabilities. Among the diverse toolkit available, payloads emerge as a critical component in both penetration testing and comprehensive security assessments. In this comprehensive guide, we …
In the ever-evolving landscape of cybersecurity, where threats loom at every turn, having the right tools is paramount. While traditional security software plays a vital role, browser extensions add a unique layer of protection and enhancement for both cybersecurity professionals …
Are you ready to take your cybersecurity skills to the next level? Do you want to uncover hidden information with just a few clicks? The Black Tiger, a powerful OSINT tool, is here to make your cyber-investigations more efficient and …
YouTube is a great platform for watching videos, but the ads can be annoying. That’s why many people use ad blockers to prevent ads from playing. However, YouTube has recently started implementing anti-adblocker measures that can prevent users from watching …