Most Popular Posts
How to Reverse trace emails on the internet – Complete Guide
Are you worried about spam or probably malicious inquiry by someone pretending to be your client? There fear not we are here to help you find the truth. Many times you will get fake emails asking for compensation or claiming

Social Engineering Attacks
Social engineering attack is a type of cyber attack that uses psychological manipulation to trick individuals into divulging sensitive information or performing actions that benefit the attacker. These attacks can be incredibly effective, and their consequences can range from stolen
Top 10 Hidden Camera Detector Apps for iPhone
Cameras have become an important part of our day-to-day life let it be capturing your precious moments or taking a selfie after a long working day brings a separate glow to your face. But like all other useful inventions, it

How to Hack Windows with a Text File
Welcome to another windows hacking tutorial using Metasploit and a text file. Yes, you heard that right, we will be using a text file to hack windows 10. How does windows hacking with a text file work? This hack uses

What are The Best Cybersecurity Measures in 2023?
Cybersecurity must be your primary goal in 2023 because there’s an influx of hacking attempts. The prime target is data breaches, and there’s an unprecedented increase in automotive hacking due to the introduction of autonomous vehicles. So, the question is

How to make advanced Phishing URLs with URLCadiz
Hackers can easily hack any device by combining social engineering, one of the most dangerous skills in their arsenal, with phishing. They mostly target individuals who are less advanced or knowledgeable on the technological side with phishing scams. Businesses and

How to Change/ Restore IMEI Number of an Android Phone without Root
IMEI numbers use to be one of the hardest things to change in your mobile device. Well not anymore. You can now easily change and restore your IMEI number without root using free-to-download play store apps. Sounds a bit too

The Evolution of Blockchain: Part 2
Having established a foundational understanding of blockchain technology in our previous segment (Blockchain Fundamentals) , let’s now delve even deeper into its transformative impact across various sectors. Our journey takes us directly into the heart of blockchain’s potential, thereby unveiling

The World of People OSINT
Peering Behind the Curtain : The World of People OSINT In today’s digital age, the internet is awash with information about people. Countless sources of information exist that people can use to gain insight into a person’s life, ranging from
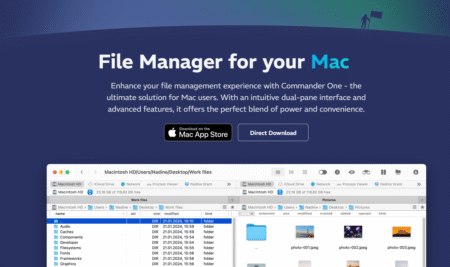
Top 10 Screen Sharing Apps For Mac OS
In the age of remote work, professionals are transforming their workspaces from offices to homes. Virtual connectivity, presentations, and interactive team sessions have become integral to maintaining workflow consistency. Screen sharing applications play a vital role in delivering effective presentations

Dirbuster: Your Guardian Angel in the World of Cybersecurity
Cybersecurity has become a battlefield, and every organization is arming itself with powerful tools to protect its digital assets. In this relentless struggle, a tool named Dirbuster stands out as a formidable weapon. In this blog post, we will dive

How to hack Android device with ADB (Android debugging bridge )
In this article, I am going to show you how easy it is to hacking android phones using only one tool which is the Android Debugging bridge. ADB is meant for developers to test and make new android apps and